How to remove a hacker from my phone: codes to unlock my phone.
How to remove a hacker from my phone: codes to unlock my phone.
Our phones play a huge role in our day to day activities, but your phone acting weird can raise a lot of questions. The thing is, your phone might have been hacked by a hacker and you need to remove that hacker as soon as possible.
If you have experienced this, I think you know how frustrating it is, but if you haven’t, then this article is definitely for you. Read this article carefully to learn how to remove a hacker from yours if it ends up being hacked.
Hacking your phone entails the unconscious download of spyware that relays real-time information about your plans. This information may include obtaining your login information and passwords. The easiest way to infect smartphones is to infect them with malware.
How to remove hacker from my phone
If you want to remove the hacker from your phone, please factory reset and install the updated version. operating system from the service provider.
If you suspect that your phone has been hacked, the first thing you need to do is go to your phone settings and then security. After that, go to the security section and then check the device administrator, where most spy apps should be able to take control of your mobile device.
Hence, by checking there first, you should be able to resolve the issue. However, you can take a different approach by downloading specific apps that should help you learn more about all the apps on your phone, what they are, what they do, and where they download from.
Another way to find out if your phone has been hacked is to turn off the internet connection on your phone and watch the amount of data consumed by your phone
How can I find a hacker on my phone?
If your phone is running slowly or your battery is draining fairly quickly, your phone may have been jailbroken. They may also mean that your phone needs an update.
Another way to know if your phone has been hacked is through excessive data consumption. It may simply mean that a dodgy application is sending data to the source.
I realized that your ability to identify the person responsible for hacking your phone depends a lot on the type of threat. To have a clearer idea of who the suspect might be, you need to figure out how your phone was compromised.
How do I run a security check on my phone?
To answer this question, I would refer to it based on two categories: iPhone devices and Android devices.
iPhone: You can run a security scan on your iPhone using certain apps that should alert you if your iPhone has been stolen. However, the ability of security software to detect a spy app on your phone depends a lot on how effective and sophisticated such apps can be. That’s why you should always buy updated security software as soon as it’s released.
Android: Viruses are not that hard to find on the Internet. Such apps usually have system-level access to some pretty detailed information about your device activity, including the messages you write and your GPS location.
In addition, you may need to physically download them to your device. This means that if you find them on your device, they have probably been installed by someone with access to your mobile device.
You have a pretty good chance of finding out who around you would like your phone to be controlled (it could be your jealous partner)
So that you can determine if there is any malware on your phone or if someone is spying on text messages. make sure you download certain antivirus applications that should be able to detect such malware.
Other things to watch out for
When it comes to the security of your phone, it needs to be dealt with immediately.
1. Take a close look at your list of applications.
The first thing I would recommend you do is look at the apps on your phone to identify apps that you may not have downloaded yourself.
Make sure any of these apps have a negative review indicating malware. If so, such applications may have been hacked by a hacker who may not be directly targeting you, but simply hunting for as much data as possible.
2. What does your phone bill say?
If you’re being charged for text messages you didn’t send or calls you never made, it’s likely that malware is infiltrating your device. This type of malware makes your phone send or receive text messages.
Also, if you get certain text messages all the time, you should send stop to those numbers. If that doesn’t work, however, you may need to call your network provider to have them block the number.
You should also consider blocking any third party messaging apps. Block other apps that might have been installed before the phone started sending text messages.
3. View the call list.
If you have done everything I have suggested so far and still feel like someone is invading your personal space, you should know that apps are not the only channel for malware to enter. Have you received a random call recently? People who get called claiming to have won an award could be victims of someone trying to hack them with a voice call.
4. When was the last time you used public Wi-Fi?
Statistics have shown that every fourth access point is usually insecure. Also, the ones that are password protected could be created by someone with an illegal motive.
So if your phone is not protected by a VPN and you are connected to an unsecured public internet source, you could be being spied on by someone who may have collected sensitive information when you log into your email.
What to do if your phone is hacked?
If you have carefully read the directions I have carefully laid out for a hacked phone and you think you might be a victim of a hacker, here are a few things to do in order to remove a hacker from your phone.
1. Reset to factory settings
Sounds pretty obvious, right? Well, to be clear, this is one of the most important steps to deal with malware issues. Once you have to remove suspicious malware from your phone and still suspect it is present, you must do so.
For your android device just go to settings then advanced system then you should go to reset option and wipe all data. For your iPhone, go to settings and choose “General”, click “Reset” and choose to delete all content.
2. Remove suspicious applications.
It’s not a guaranteed way to fix all of your performance issues, but it’s the right move. It’s always a good idea to uninstall any apps that might have been detected as malware during a scan.
3. Is your information public?
Some malware and hacks usually cause little to no symptoms, and more often than not, people only notice when their digital services are affected. Some only notice this when they become victims of a scam where hackers use their personal information to set up lines of credit.
There are several tools you can use to make sure your data has been compromised. Some of them are paid, others are free.
Codes to track and remove a hacker from your phone
You can immediately check if your phone has been hacked, or if your calls, messages, etc. have been forwarded without your knowledge. All you have to do is dial some USSD codes – ##002#, *#21# and *#62# from your phone’s dialer to confirm that your phone has been hacked.
002 ## # – If your voice, data or SMS call is forwarded, dialing this USSD code will erase them.
* # # 21 – By dialing this USSD code, you will know if your calls are redirected somewhere else or not.
*##62 – With it, you can find out if any of your calls – voice, data, fax, SMS, etc. have been forwarded or forwarded without your knowledge.
If you find this article helpful, you can share it with your friends and don’t forget to leave a comment and follow more educational blog posts on our site.
Prevent Your Phone From Hacking | Android Secret Codes
Today i share with you some codes to check and prevent your android device from hacking:
Data the most important factor of everyone life. No one does want that his/her personal data are gone in wrong hand. In today world, where the technology is become more and more advanced. Where it’s latest cracks and vulnerabilities are also introduced daily. We also download many applications in our Android phones. Some are from authentic sources and some are from unauthentic sources, where the risk of malwares and breach of personal data are become 90%. Because the attackers attached the malicious files with pirated softwares and when the user download it. The attackers make control on their victim device and transfer all personal data to their devices.
But the question is how we see our Android device are in attackers control or not???
So, today i answer this question and tell you some codes which can tell you that your android device are in attackers control or not.
•: Android Secret Codes
If you want to use these codes first open your android device call pad and type the following codes, which have different purposes:
- To Check your android device is hacked or not. Type *#21*, *#67# or *#62# in your phone call dialing pad. The purpose of these three codes are same but most time one code is valid to the device and other is not valid. When you enter one of these codes press the dial phone icon button (which is used to call others). After this the following display is appear on your screen.
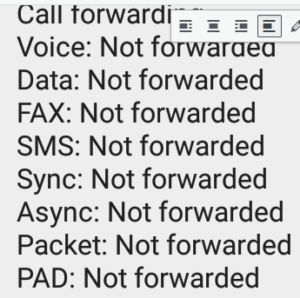
This display will show you, your device is hacked or not. If your device is in attackers control or if the attacker transferred your messages, calls, personal data or voices etc. So, you can see forwarded instead of not forwarded.
Now another question is raised in your mind is if the attackers take control of our device and if this option show forwarded instead of not forwarded. So, what we can do???
Don’t worry i also tell you another code which can solve your problem.
- If your android device is in attackers control and they can forward your personal information. So type ##002# in your android dial pad and press the phone icon button (which is used to call others). After this you can see the following display.
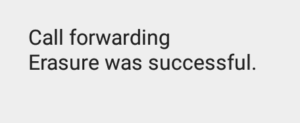
In this display you can see a line “Erasure was successful”. This mean if the attackers forward your personal information. So, this code disabled their attack.
•: My Opinion:
I hope you like these codes. Give me your opinion about these codes in comment section. Always take one thing in your mind no data is small and if you don’t focus on your privacy. So, one day you will trap in some serious problem.
•: Ending
I hope after reading this article you can know about how to prevent your android device from hacking with the help of secret codes. This is my opinion about this topic. If i can take any mistake please comment me and i am waiting for your response.

